Free & Easy Returns
Best Deals
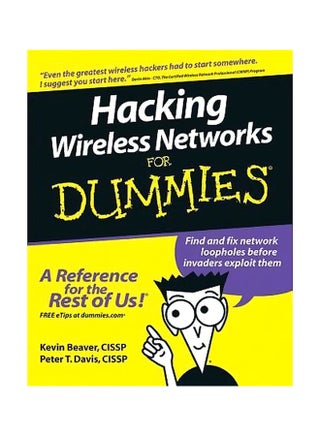
| Publisher | John Wiley And Sons Inc |
| ISBN 10 | 0764597302 |
| Book Format | Paperback |
| Book Description | This book enables readers to become a cyber hero and know the common wireless weaknesses. "Reading a book like this one is a worthy endeavor toward becoming an experienced wireless security professional." - Devin Akin CTO, The Certified Wireless Network Professional (CWNP) Program. Wireless networks are so convenient not only for you, but also for those nefarious types who'd like to invade them. The only way to know if your system can be penetrated is to simulate an attack. This book shows you how, along with how to strengthen any weak spots you find in your network's armor. Discover how to: perform ethical hacks without compromising a system; combat denial of service and WEP attacks; understand how invaders think; recognize the effects of different hacks; and protect against war drivers and rogue devices. |
| Publication Date | 13 September 2005 |
| ISBN 13 | 9780764597305 |
| Author | Kevin Beaver, Peter T. Davis |
| Language | English |
| About the Author | Kevin Beaver, CISSP, is a 16-year specialist in security assessments and incident response. Peter T. Davis, CISSP, has worked with information systems audits and security for 24 years. |
| Number of Pages | 384 |